Android Debug Bridge
 | |
 Starting the adb server in GNOME Terminal, which then enumerates the devices. After that, a shell to the OnePlus 5 is opened to run the uname command. | |
| Original author(s) | |
|---|---|
| Stable release | 31.0.3
|
| Repository | android |
| Written in | C++ |
| Operating system | Windows, Linux, macOS |
| Included with | Android SDK |
| Type | Software development tool |
| License | Apache License 2.0 |
| Website | developer |
The Android Debug Bridge (commonly abbreviated as adb) is a programming tool used for debugging Android-based devices using a USB or TCP connection. The daemon on the Android device connects with the server on the host PC, which connects to the client that is used by the end-user. Made available as open source software under the Apache License by Google since 2007, features include a shell and the possibility to make backups. The adb software is compatible with Windows, Linux and macOS. It has been misused by botnets and other malicious software, for which mitigations where developed such as RSA authentication and whistlisting.
Features[]

Features of adb include copying files from the host computer,[1] installing apps, viewing logcat output, getting a Unix shell, [2] and rebooting into Qualcomm EDL mode.[3] For example, Android applications can be saved by the command backup to a file.[4] It also includes support for the Java Debug Wire Protocol.[5]
Some graphical interfaces have been made available. The graphical Android Device Monitor in Android Studio can be used for retrieving information from an Android device.[6]
Development history[]
The first release of the Android SDK was in 2007.[7] Since 2017, Google made it possible to download adb separately from the Android SDK.[8]
In 2015, Microsoft released an Android emulator that is able to connect to the adb client.[9] In 2016 for Android Studio 2.0 a 5x performance improvement was made for installing apps and pushing files through adb.[10] For easier usage of Android Things, a wrapper was made in 2017 around manual adb commands.[11] For Android 11 in 2020, Google added adb incremental installations.[12] In 2020, Wi-Fi adb was integrated into Android Studio for macOS.[13] In 2021 for Android 12, the adb backup command will be limited so that backing up user data from apps will be opt-in using a per-app manifesto configuration.[14]
Setup[]

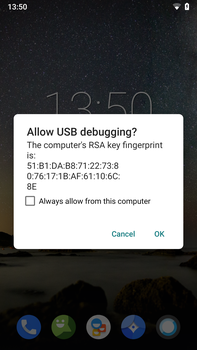
For enabling USB debugging on the Android device, it needs to be enabled in the "developer settings" window
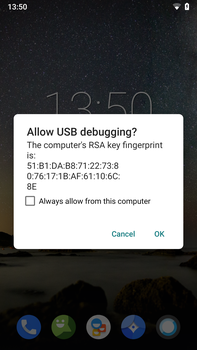
After the device is connected to the host computer, the user needs to verify the RSA key fingerprint of the host computer
Host computer[]
For Windows, the Android SDK contains the adb.exe binary that can be extracted and installed, together with the fastboot software.[15] It has been recommended by How-To-Geek to add the folder containing the binaries to the PATH environment variable.[16]
On Ubuntu, adb can be installed with the android-tools-adb package.[17] For Debian, it has been recommended to also install the android-sdk-platform-tools-common package next to the adb package, which installs the udev rules which makes it possible to run the tool without root permissions.[18] For macOS and other Linux distributions, the platform tools can be downloaded and the PATH variable can be modified in bashrc.[19]
Android device[]
In Android 4.2.2 or later (API level 17), a dialog is shown with an RSA fingerprint that the user needs to accept. This protects against computers exploiting the debugging mechanism without consent of the device user.[20] Starting in Android 4.2, the developer settings are hidden by default. Pressing seven times on the build number in the about menu makes them visible to the user. After that, the USB debugging option can be enabled.[21] The procedure does differ for some Android vendors. Huawei requires entering a pincode before adb can be enabled.[22]
If the touchscreen of an Android device is broken, it can be possible to connect a mouse to the device using USB On-The-Go and enable USB debugging.[23][22]
Architecture[]
The adb protocol can be transported over USB or over Wi-Fi through TCP. It uses a client-server architecture. There are two different protocols in use. The first is between the client and the server and the second is between the server and the daemon. The adb daemon is implemented in C and located in the Android user space. The daemon is facilitated by the Android USB framework, UsbDeviceManager and UsbDebuggingManager.[5]
Client ↔ server protocol[]
The communication mode between the client and server is a TCP socket. The server listens on a port, to which the client has to send a request. The request contains a 4-byte intial field in ASCII and a payload. The payload starts with the word host, to indicate it should be sent to the server. The server can then reply with OKAY or FAIL to indicate the status, combined with an optional payload and length.[5]
Server ↔ daemon protocol[]
The messages sent from the server consist of a 24-byte long header, with the following fields:[5]
- Command
- First argument
- Second argument
- Length of the payload, 0 or higher
- CRC32 of the data payload
- Magic value, calculated through command XOR
0xFFFFFFFF
Security[]
Up to Android 2.2, Android was vulnerable to the RageAgainstTheCage exploit. The adb daemon did not check for the return value of the setuid system call when dropping privileges. The exploit forks processes until it fails due to the exhaustion of process identifiers. When the daemon crashes and restarts, it can't start a new process with dropped privileges and keeps running as root. Then adb provided a root shell.[24]
In 2017, a security vulnerability was disclosed that exploited ADB to take over the onboard modem. The attack required adb to be already enabled and authorized, although some workarounds were available.[25] Various families of malware such as ADB.Miner, Ares, IPStorm, Fbot and Trinity have scanned the internet for public availability of the adb interface and installed malware on those devices.[26] adb can also been used to remove malware, by booting into safe mode and running the adb uninstall command.[27]
References[]
- ^ Darcey, Lauren (2012). Android wireless application development. Shane Conder (3rd ed.). Upper Saddle River, NJ: Addison-Wesley. ISBN 978-0-321-81383-1. OCLC 749852462. Archived from the original on 2021-09-26. Retrieved 2021-09-26.
- ^ "Things You Can Do with Android's adb Command". For Dummies. Archived from the original on 2018-05-15. Retrieved 2021-09-09.
- ^ EASTTOM, CHUCK (2021). An In-Depth Guide to Mobile Device Forensics. [S.l.]: CRC PRESS. p. 72. ISBN 0-367-63300-0. OCLC 1250310301. Archived from the original on 2021-09-26. Retrieved 2021-09-26.
- ^ Jack Wallen (2015-03-06). "How to create a full backup of your Android device without root". Archived from the original on 2016-01-24. Retrieved 2016-01-29.
- ^ a b c d Regupathy, Rajaram (2014). Unboxing Android USB: a hands-on approach with real World examples. Berkeley, CA. ISBN 978-1-4302-6209-1. OCLC 880673864. Archived from the original on 2021-09-26. Retrieved 2021-09-26.
- ^ Morgillo, Ivan (2016). Learning embedded Android N programming: create the perfectly customized system by unleashing the power of Android OS on your embedded device. Stefano Viola. Birmingham, UK. p. 89. ISBN 978-1-78528-328-4. OCLC 957278992. Archived from the original on 2021-09-26. Retrieved 2021-09-26.
- ^ "Google releases Android SDK". Macworld. Archived from the original on 2021-09-10. Retrieved 2021-09-10.
- ^ "Google makes ADB, fastboot, and other platform tools available without full SDK or Android Studio download". Android Police. 2017-01-05. Archived from the original on 2021-04-10. Retrieved 2021-09-09.
- ^ Vasile, Cosmin. "Microsoft Releases Android Emulator and It's Supposed to Be Faster than Google's". Softpedia. Archived from the original on 2021-09-10. Retrieved 2021-09-10.
- ^ "Android Studio 2.0 - Beta". Android Developers Blog. Archived from the original on 2021-09-10. Retrieved 2021-09-10.
- ^ "Android Things Developer Preview 6". Android Developers Blog. Archived from the original on 2021-09-10. Retrieved 2021-09-10.
- ^ "Turning it up to 11: Android 11 for developers". Android Developers Blog. Archived from the original on 2021-09-17. Retrieved 2021-09-10.
- ^ "Announcing Android Studio Arctic Fox (2020.3.1) & Android Gradle plugin 7.0". Android Developers Blog. Archived from the original on 2021-09-12. Retrieved 2021-09-10.
- ^ "Behavior changes: Apps targeting Android 12 | Android 12 Beta". Android Developers. Retrieved 2021-09-28.
- ^ "The Easiest Way to Install Android's ADB and Fastboot Tools on Any OS". Lifehacker. Archived from the original on 2021-07-18. Retrieved 2021-09-25.
- ^ Hoffman, Chris. "How to Install and Use ADB, the Android Debug Bridge Utility". How-To Geek. Archived from the original on 2021-09-18. Retrieved 2021-09-09.
- ^ Smyth, Neil (2020). "7". Android Studio 4. 0 Development Essentials - Java Edition: Developing Android Apps Using Android Studio 4. 0, Java and Android Jetpack. Cary. ISBN 978-1-951442-21-7. OCLC 1190906409. Archived from the original on 2021-09-26. Retrieved 2021-09-26.
- ^ "Debian -- Details of package adb in bullseye". packages.debian.org. Archived from the original on 2021-09-08. Retrieved 2021-09-08.
- ^ "How to Install Android Debug Bridge (ADB) and Fastboot". Lifewire. Retrieved 2022-01-18.
{{cite web}}: CS1 maint: url-status (link) - ^ "Run apps on a hardware device". Android Developers. Archived from the original on 2021-09-08. Retrieved 2021-09-08.
- ^ Wallen, Jack. "How to enable Developer options in Android 4.2". TechRepublic. Archived from the original on 2021-09-09. Retrieved 2021-09-09.
- ^ a b Aranzulla, Salvatore. "Come attivare debug USB". Salvatore Aranzulla (in it-IT). Archived from the original on 2021-09-09. Retrieved 2021-09-09.
{{cite web}}: CS1 maint: unrecognized language (link) - ^ Ogubuike, Udochi (2019-08-09). "How to enable USB debugging mode on Android". The Punch. Archived from the original on 2019-09-17. Retrieved 2021-09-09.
- ^ Drake, Joshua J. (2014). Android hacker's handbook. Zach Lanier, Collin Mulliner, Pau Oliva, Stephen A. Ridley, Georg Wicherski. Indianapolis, IN: Wiley. p. 75. ISBN 978-1-118-60861-6. OCLC 875820167. Archived from the original on 2021-09-26. Retrieved 2021-09-26.
- ^ Mendelsohn, Tom (2017-01-09). "Google plugs severe Android vulnerability that exposed devices to spying". Ars Technica. Archived from the original on 2021-09-10. Retrieved 2021-09-10.
- ^ Cimpanu, Catalin. "Android devices ensnared in DDoS botnet". ZDNet. Archived from the original on 2021-09-10. Retrieved 2021-09-10.
- ^ Schuman, Evan. "This Vultur app takes malicious to the next level". Computerworld. Archived from the original on 2021-09-10. Retrieved 2021-09-10.
External links[]
- Android (operating system)
- Debugging
- Communications protocols
- Android (operating system) development software